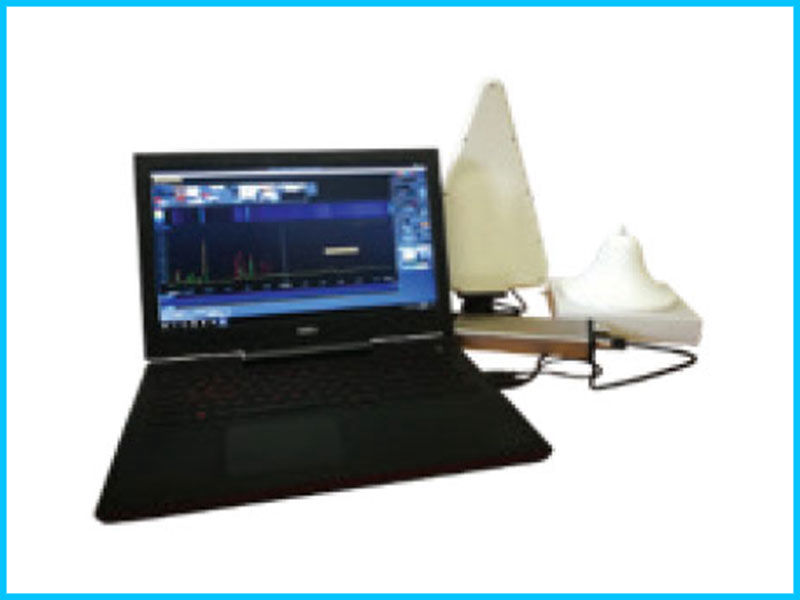
OSCOR™ Blue Spectrum Analyzer
The OSCOR Blue is a portable spectrum analyser with a rapid sweep speed and functionality suited for detecting unknown, illegal, disruptive, and anomalous rogue transmissions across a wide frequency range. The OSCOR Blue Spectrum Analyzer is designed to detect illicit eavesdropping signals, perform site surveys for communication systems, conduct radio frequency (RF) emissions analysis, and investigate misuse of the RF spectrum.
Detailed Information: https://reiusa.net/rf-detection/oscor-blue-spectrum-analyzer/